Quantum Threat Preparedness Framework (QTPF): The Complete Roadmap to Protect Your Systems Before Quantum Attacks Become Reality
Bottomline: Quantum threats are coming. Organizations that prepare early with structured frameworks will adapt faster, reduce risk, and protect long-term data integrity.
Introduction to the Quantum Threat Preparedness Framework
Quantum computing is advancing at a pace that requires long-term security planning today rather than reactive measures later. While current encryption systems remain functional, emerging quantum capabilities are expected to challenge the mathematical foundations that protect modern digital infrastructure.
Organizations rely heavily on encryption to secure communications, protect financial transactions, verify identities, and preserve sensitive data. When quantum computing reaches sufficient maturity, some widely used encryption methods may become vulnerable. Preparing for that shift requires structured planning rather than isolated technical fixes.
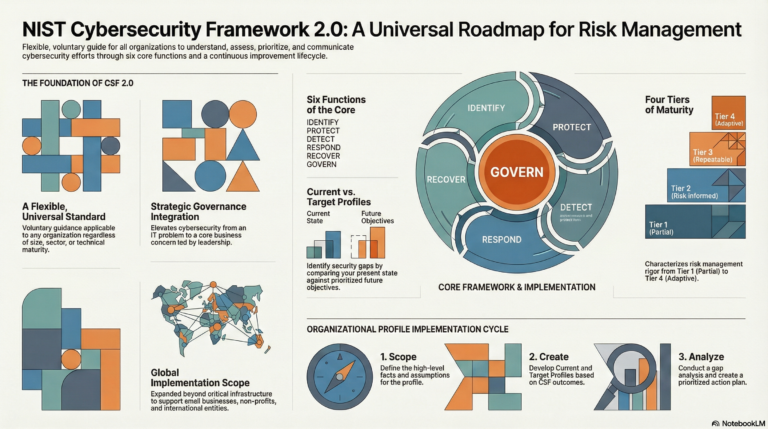
The Quantum Threat Preparedness Framework, often referred to as QTPF, provides a systematic roadmap for organizations seeking to strengthen their long-term security posture. It supports the transition from awareness to measurable readiness through clearly defined phases, governance roles, and implementation models.
Rather than waiting for disruptive breakthroughs, organizations can use QTPF to build adaptable security systems capable of evolving alongside technological advancements.
What Is the Quantum Threat Preparedness Framework
The Quantum Threat Preparedness Framework is a structured methodology used to prepare digital environments for future quantum-enabled risks. It establishes consistent processes that allow organizations to identify cryptographic dependencies, classify risk exposure, and implement controlled migration strategies.
The framework operates on five foundational principles.
Visibility into cryptographic assets
Risk-based prioritization
Cryptographic agility
Gradual migration
Continuous adaptation
These principles transform quantum readiness from a conceptual concern into an operational discipline supported by measurable progress indicators.
QTPF applies across multiple organizational roles including security teams, enterprise architects, compliance leaders, infrastructure engineers, and technology executives. Each role contributes to maintaining secure digital ecosystems capable of withstanding future computational advances.
Why Organizations Need a Quantum Threat Framework
Most modern digital systems rely on encryption algorithms originally designed for classical computing environments. Quantum computing introduces computational methods capable of solving certain mathematical problems at speeds far beyond traditional systems.
The most significant risk is not immediate encryption failure but delayed exposure of sensitive information. Adversaries may capture encrypted data today and store it until quantum capabilities allow decryption in the future. This scenario creates long-term vulnerability for organizations that maintain sensitive records.
Without a structured framework, organizations often encounter several critical challenges.
Unidentified encryption dependencies
Legacy infrastructure that cannot be easily upgraded
Unexpected migration complexity
Regulatory compliance risk
Loss of trust due to data exposure
Implementing a formal preparation framework reduces uncertainty and enables strategic planning across multiple operational layers.
The Core Objectives of QTPF
Every framework exists to achieve measurable outcomes. The Quantum Threat Preparedness Framework focuses on strengthening resilience across both technical systems and governance processes.
Key objectives include identifying cryptographic assets across all systems, understanding which data requires long-term confidentiality, reducing reliance on vulnerable encryption algorithms, enabling rapid transition to quantum-resistant technologies, and maintaining operational continuity during system upgrades.
Achieving these objectives requires consistent monitoring, cross-functional collaboration, and clearly defined accountability.
Quantum Threat Readiness Self-Assessment
Understanding readiness requires measurable evaluation. This self-assessment enables organizations to evaluate their preparedness level and identify areas that require improvement.
Score each item using the following scale.
0 indicates Not Started
1 indicates In Progress
2 indicates Completed
Cryptographic Inventory Readiness
All encryption assets identified
Certificate usage documented
Key storage locations mapped
Legacy encryption dependencies identified
Risk Classification Readiness
Data sensitivity categories defined
Long-term data retention requirements documented
High-value systems identified
Regulatory data requirements mapped
Cryptographic Agility Readiness
Encryption services designed as modular components
Centralized key management implemented
Algorithm replacement procedures documented
System architecture supports cryptographic upgrades
Post-Quantum Preparedness Readiness
Post-quantum cryptography pilot testing initiated
Vendor quantum readiness evaluated
Migration roadmap documented
Security teams trained on quantum risks
Scoring Interpretation
Scores between 0 and 10 indicate high exposure risk and minimal readiness
Scores between 11 and 20 indicate moderate readiness with capability gaps
Scores between 21 and 30 indicate structured preparation underway
Scores between 31 and 40 indicate strong readiness and advanced planning maturity
Organizations should perform periodic reassessment to track readiness improvements.
Phase 1 Cryptographic Discovery
Cryptographic discovery establishes visibility into encryption usage across all systems. Without complete discovery, organizations risk overlooking hidden dependencies that later disrupt migration planning.
Discovery activities typically include identifying encryption libraries, certificate usage, authentication systems, database encryption modules, network communication protocols, application security components, and backup archives.
Many organizations discover undocumented encryption dependencies during this phase. Documenting these dependencies improves risk awareness and enables more accurate planning.
Phase 2 Risk Classification and Prioritization
After identifying encryption dependencies, organizations must determine which systems require immediate attention.
Risk classification organizes systems according to sensitivity, operational importance, and expected data retention duration.
Primary classification factors include data sensitivity, regulatory obligations, operational criticality, and long-term confidentiality requirements.
High-priority systems often include identity management systems, financial transaction systems, intellectual property repositories, and regulatory data storage platforms.
Lower-priority systems may include short-term operational logs or publicly accessible data.
Prioritization ensures that resources are allocated where they deliver the greatest security benefit.
Quantum Threat Risk Matrix
Risk matrices provide structured clarity for decision-making and help organizations identify where migration efforts should begin.
Risk Level Low
Description Systems containing short-lived or public data
Recommended Action Monitor developments and prepare future upgrades
Risk Level Moderate
Description Systems supporting internal operations or limited retention data
Recommended Action Begin planning for cryptographic upgrades
Risk Level High
Description Systems containing confidential or regulated information
Recommended Action Prioritize migration readiness and testing
Risk Level Critical
Description Systems protecting long-term strategic, financial, or national security data
Recommended Action Initiate immediate planning and early adoption strategies
This structured classification supports leadership teams responsible for allocating security investments.
Phase 3 Cryptographic Agility Design
Cryptographic agility enables organizations to replace encryption algorithms without rebuilding entire systems. This capability reduces long-term migration cost and complexity.
Agility design focuses on modular encryption services, centralized key management systems, configurable algorithm libraries, and version-controlled security policies.
Systems designed with agility can adapt to emerging cryptographic standards with minimal operational disruption.
Organizations that implement agility early gain flexibility and long-term cost efficiency.
Phase 4 Post-Quantum Cryptography Evaluation
Post-quantum cryptography introduces encryption algorithms designed to resist quantum-enabled attacks. This phase focuses on testing candidate algorithms within controlled environments.
Evaluation criteria include system compatibility, processing performance, network overhead, key storage requirements, and operational reliability.
Organizations often begin with hybrid encryption models that combine classical and quantum-resistant methods. Hybrid deployment allows gradual transition while maintaining operational stability.
Pilot testing environments should simulate real-world conditions to ensure accurate performance validation.
Phase 5 Migration Strategy and Execution
Migration represents one of the most resource-intensive phases within the framework. It requires careful sequencing to avoid operational disruption.
Typical migration activities include updating encryption libraries, rotating keys, replacing certificate infrastructures, modifying authentication mechanisms, and validating compatibility across dependent systems.
Incremental rollout strategies reduce risk by allowing phased implementation rather than large-scale simultaneous deployment.
Migration planning must also consider vendor readiness and legacy system compatibility.
Phase 6 Continuous Monitoring and Adaptation
Quantum preparedness is not a one-time event. It requires continuous monitoring to ensure long-term resilience.
Monitoring activities include tracking advancements in quantum computing technology, evaluating emerging cryptographic standards, updating encryption policies, maintaining accurate cryptographic inventories, and conducting periodic security reviews.
Continuous adaptation ensures that organizations remain secure as technology evolves.
Quantum Threat Preparedness Maturity Model
A maturity model provides measurable visibility into organizational readiness and helps leadership plan long-term improvements.
Level 1 Awareness
Organizations recognize quantum-related risks but have not initiated structured preparation activities.
Level 2 Discovery
Encryption dependencies are documented and visibility into cryptographic usage improves across operational environments.
Level 3 Prepared
Risk classification and migration strategies are defined. Teams begin evaluating quantum-resistant technologies.
Level 4 Agile
Cryptographic agility is implemented across major systems, allowing algorithm replacement without major disruption.
Level 5 Quantum Ready
Post-quantum cryptography is deployed across critical infrastructure with continuous monitoring capabilities.
Organizations should aim to progress gradually through maturity levels rather than attempting rapid transformation.
Industry Sectors Most Impacted by Quantum Threats
Certain industries face higher risk exposure due to long data retention requirements and strict regulatory obligations.
Financial institutions rely heavily on secure transaction processing and identity verification systems.
Healthcare organizations must protect sensitive patient data that remains confidential for extended periods.
Government agencies maintain classified information requiring decades of protection.
Cloud service providers manage multi-tenant environments that store large volumes of encrypted data.
Technology companies rely on digital signatures to maintain software integrity and secure update mechanisms.
QTPF Governance Framework
Governance ensures that quantum preparedness efforts remain coordinated across technical and administrative teams.
Chief Information Security Officer
Responsible for defining quantum security strategy, approving budgets, and ensuring alignment with risk management objectives.
Enterprise Architect
Responsible for designing cryptographic agility models and ensuring architectural compatibility with future quantum-resistant technologies.
Cryptography Lead
Responsible for evaluating encryption algorithms, managing cryptographic inventories, and guiding migration planning.
Compliance Officer
Responsible for aligning quantum readiness initiatives with regulatory standards and documenting compliance requirements.
Infrastructure Engineers
Responsible for implementing system updates, configuring encryption modules, and supporting post-quantum deployment activities.
Clear governance structures ensure that preparedness becomes an ongoing operational capability.
Strategic Benefits of Implementing QTPF
Organizations implementing QTPF gain multiple strategic advantages beyond security improvements.
Benefits include improved system visibility, stronger security posture, reduced long-term upgrade costs, increased regulatory readiness, enhanced customer trust, and improved infrastructure resilience.
Framework-driven preparation also supports digital modernization initiatives that extend beyond cybersecurity.
Frequently Asked Questions
What is the primary goal of the Quantum Threat Preparedness Framework?
The primary goal is to help organizations identify cryptographic risks, prioritize sensitive systems, and transition to quantum-resistant technologies using structured processes.
How soon should organizations begin implementing QTPF?
Preparation should begin as early as possible because migration timelines often span multiple years.
Which systems should be prioritized first?
Systems protecting long-term sensitive data or supporting mission-critical operations should be addressed first.
Is post-quantum cryptography available today?
Yes. Several post-quantum cryptographic algorithms exist and are currently being standardized and tested across industries.
Can small organizations benefit from QTPF?
Yes. Smaller organizations benefit from early planning because it reduces long-term disruption and upgrade complexity.
Will all encryption become obsolete?
Not all encryption will fail, but widely used algorithms such as RSA and elliptic curve cryptography are expected to require replacement over time.
The Future of Security in the Quantum Era
Quantum computing represents a significant shift in computational capability that will influence security architecture for decades.
Organizations that adopt structured preparation frameworks gain the ability to adapt rather than react. The Quantum Threat Preparedness Framework provides a comprehensive roadmap that supports discovery, prioritization, design, migration, and long-term monitoring.
Preparing today ensures resilience tomorrow. Framework-driven readiness transforms uncertainty into structured action and positions organizations to operate securely in an evolving technological landscape.