NIST Cybersecurity Framework Explained: A Practical Guide for Modern Organizations
NIST Cybersecurity Framework Explained
Imagine getting a phone call at 2:00 a.m. notifying you that your organization’s critical data has been locked by a ransomware attack. For many business leaders, this is their worst nightmare. In a digital landscape where supply chain attacks, phishing, and automated threats are everyday realities, hoping you won’t be a target is no longer a valid strategy.
But where do you start? Cybersecurity can feel like a bottomless pit of technical jargon, expensive tools, and endless checklists.
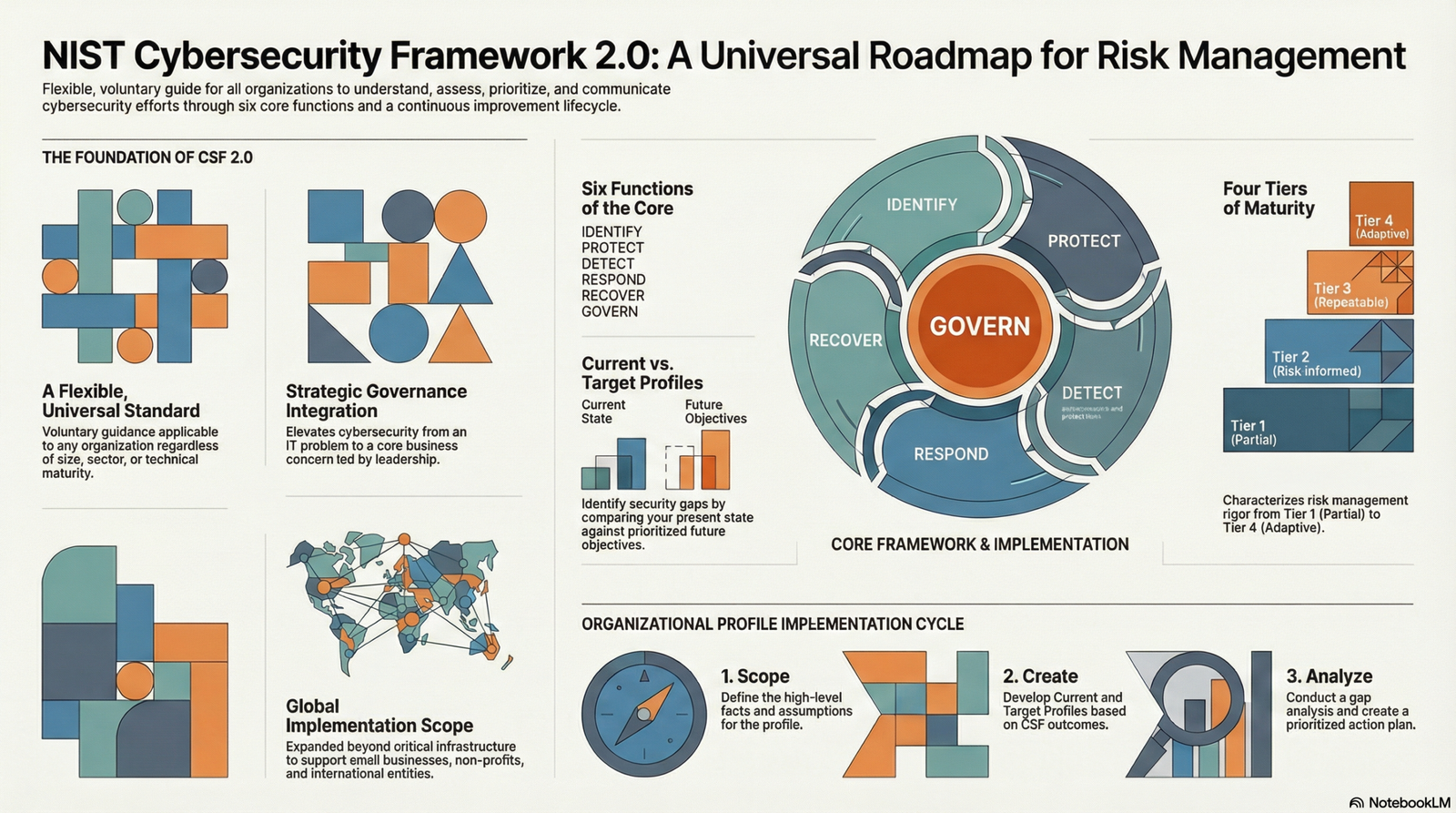
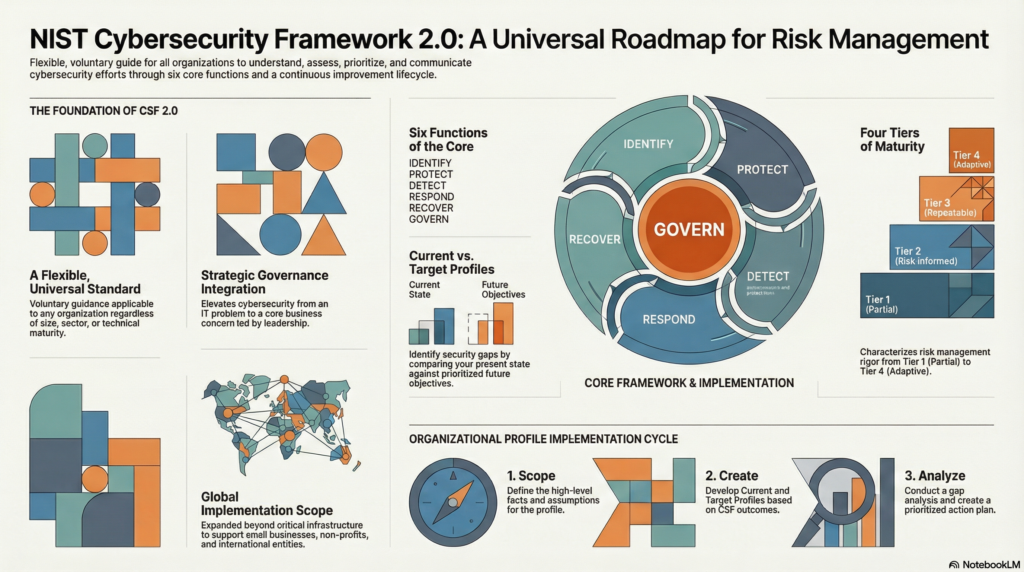
Enter the NIST Cybersecurity Framework (CSF) 2.0. Developed by the National Institute of Standards and Technology, the CSF is not a rigid regulatory mandate—it is a voluntary, flexible, and beginner-friendly blueprint designed to help organizations of all sizes manage and reduce their cyber risks. Whether you are a local school district or a global enterprise, the NIST CSF provides a common language that aligns your technical IT teams directly with your executive board.
Here is your practical guide to understanding and implementing the NIST CSF 2.0.
The Blueprint: The Six Core Functions
At the heart of the NIST CSF is the “Core,” which breaks down complex cybersecurity tasks into a continuous lifecycle of six high-level functions. Think of these as the engine that drives your entire security strategy:
- Govern: The newest addition to version 2.0, this function puts cybersecurity squarely on the shoulders of leadership. It involves setting policies, managing third-party supply chain risks, and understanding your legal and regulatory requirements.
- Identify: You cannot protect what you do not know you have. This step involves creating inventories of your physical devices, software, sensitive data, and network connections to understand your actual risk exposure.
- Protect: This is where you put up the shields. It includes deploying safeguards like Multi-Factor Authentication (MFA), encrypting data, and training your employees to spot phishing emails.
- Detect: Assuming your defenses will eventually be breached, how fast will you notice? This function focuses on continuous monitoring and using tools to spot anomalies and malicious activity in real-time.
- Respond: When an attack happens, you need a plan. This step outlines how to contain the threat, eradicate the attackers, and communicate with stakeholders and law enforcement.
- Recover: After the fire is put out, how do you get back to business? This involves restoring from clean backups, repairing systems, and reviewing lessons learned so it doesn’t happen again.
The Workflow: How to Actually Use the Framework
The real magic of the NIST CSF lies in its Organizational Profiles. A profile is simply a snapshot of your cybersecurity posture. The framework provides a straightforward, 5-step workflow to help you map your journey from where you are today to where you need to be:
Step 1: Scope the Profile Decide what you are evaluating. Are you looking at the entire organization, or just a specific department, like HR or the manufacturing floor?
Step 2: Gather Information Collect your existing organizational policies, hardware/software inventories, and legal compliance requirements (like HIPAA or SOC2).
Step 3: Create the Organizational Profiles You will create two profiles:
- Current Profile: An honest assessment of what you are doing right now. (e.g., “We only require passwords for login.”)
- Target Profile: Where you want to be based on your business risks. (e.g., “We require Multi-Factor Authentication for all accounts accessing sensitive data.”)
Step 4: Analyze Gaps and Create an Action Plan Compare the Current Profile against the Target Profile. The missing pieces are your “gaps”. Create a prioritized list of actions to fix them, keeping your budget and staff bandwidth in mind.
Step 5: Implement the Action Plan Execute your plan, track your progress, and continuously update your profiles as you improve.
Automating the Framework with Modern Tools
You don’t have to manage this framework using just clipboards and spreadsheets. Modern cybersecurity relies heavily on automation and Artificial Intelligence to help manage the sheer volume of data and threats.
For example, during the Detect and Respond phases, tools like Microsoft Sentinel or Splunk can use AI to identify a compromised account and automatically lock it down within seconds—drastically reducing the damage an attacker can do.
AI and Automation Tools in Modern Cybersecurity and Business
| Use case | What the AI/automation tool does | Input type | Output type | Why this matters for AI & Automation Tools in Modern Cybersecurity and Business |
|---|---|---|---|---|
| Automated Threat Detection & Incident Response (e.g., Microsoft Sentinel) | Uses built-in analytics rules and AI to detect suspicious behavior and triggers automation playbooks. | Logs collected from across the environment, including cloud, on-premises, Microsoft 365, and third-party sources. | Real-time alerts and automated containment actions, such as instantly isolating a compromised device or disabling a user account. | Allows for instant response to threats 24/7 (even at 2:00 a.m.), drastically reducing a business’s exposure during an attack and saving valuable time. |
| Security Workflow Orchestration (e.g., Cortex XSOAR, Splunk, ServiceNow) | Creates customized, automated workflows to manage and respond to security incidents. | Security alerts and network event data across mixed or non-Microsoft environments. | Automated execution of defense steps, including collecting evidence, blocking malicious IPs, or updating IT tickets. | Standardizes the response process, replacing manual human intervention with fast, consistent procedures every time an incident occurs. |
| Automated Asset & Data Discovery (e.g., Defender for Endpoint, Varonis, AWS Config) | Automatically scans environments to discover devices on a network (even unmanaged ones), inventory cloud resources, and find and classify sensitive data. | Network connections, file shares, and cloud storage environments. | Dynamic asset inventories and data classification labels applied to sensitive information. | Shifts businesses away from manual, error-prone spreadsheets to a data-driven visibility model, ensuring you always know exactly what assets exist and need protecting. |
| Content Creation & Presentation Design (e.g., Oreate AI) | Acts as an all-in-one AI assistant to write essays, build presentations, paraphrase, and humanize content. | User text prompts and raw data/ideas. | Plagiarism-free written content, professional presentations, and humanized text. | Automates time-consuming formatting, design, and writing tasks, giving professionals a smart tool to generate clear communications, marketing materials, or internal guides rapidly. |
A Practical Example: Rockford Public Schools
To see this in action, look no further than Rockford Public Schools in Illinois. In 2019, the district suffered a devastating ransomware attack.
Instead of just applying a band-aid, their IT leadership used the NIST framework to completely overhaul their strategy. They mapped out a modernized data center, standardized their IT infrastructure across 41 schools, and implemented strict security policies to eliminate vulnerabilities. By aligning their recovery and protection efforts with NIST, they transformed a crisis into a highly secure, future-proofed environment capable of supporting new technologies like AI and Wi-Fi 6 for their 27,700 students.
Building a Phased Roadmap
If you are a beginner, do not try to do everything at once. Attempting to build a perfect, enterprise-grade security program overnight is a recipe for burnout. Instead, use a phased approach:
- Phase 1 (The Basics): Roll out Multi-Factor Authentication (MFA), ensure your data is backed up, and start training your employees.
- Phase 2 (Visibility): Introduce centralized logging, continuous monitoring, and automated incident response tools.
- Phase 3 (Continuous Improvement): Begin conducting regular risk reviews and penetration testing.
Cybersecurity Resilience
Cybersecurity is no longer just an IT problem; it is a fundamental business enabler. The NIST Cybersecurity Framework 2.0 strips away the intimidation factor, offering a clear, scalable roadmap to protect your assets, your reputation, and your bottom line.
Remember, the goal of the NIST CSF isn’t to achieve 100% perfect security—because that doesn’t exist. The goal is resilience. By governing your strategy, identifying your risks, and preparing to detect and respond to the inevitable, your organization can face the modern digital landscape with confidence.